Why an IP Address Can Be Valid but Useless
When working with proxies, many users look at only one indicator – whether the IP address is valid. If the proxy responds to a request and returns a correct IP, it is usually considered working. However, in practice this is often not enough. Sometimes an IP address passes basic checks without any issues but still turns out to be of little use for real tasks. This becomes especially noticeable in scenarios where proxies are used for automation, web scraping, API interactions, or handling a large number of requests. In such situations, the availability of the IP alone is not what matters most. Its reputation, origin, and behavior within the network also play a significant role.
Let’s examine why a valid IP does not always mean a usable IP and which factors influence this.
Why a Valid IP Does Not Guarantee Stable Performance
In a basic sense, a valid IP is an address that:
- responds to connection requests
- can send HTTP requests
- is not explicitly blocked
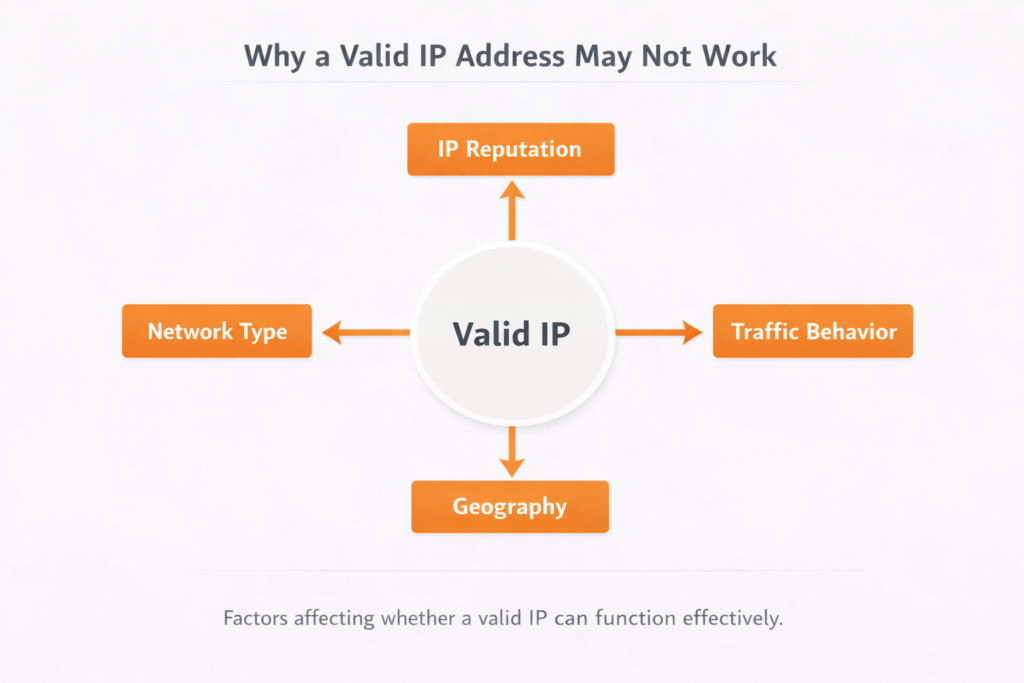
However, modern anti-fraud systems evaluate IP addresses using a much more complex set of signals.
These include:
- IP usage history
- network type
- geographic location
- request frequency
- traffic behavior
Because of this, a technically working proxy may still perform poorly when interacting with specific services.
IP Reputation and Usage History
One of the key factors is the reputation of the IP address.
If an IP was previously used for:
- aggressive scraping
- large-scale account registrations
- suspicious request patterns
it may already be present in internal filtering systems used by online services.
At the same time, such IPs may still:
- pass basic proxy checks
- show normal latency
- open websites in a browser
However, when used through APIs, automated scripts, or scraping tools, they may quickly encounter restrictions.
This is why professional infrastructures often rely on residential proxies, as these IPs resemble typical user connections.
Proxy Type and Its Impact on Detection
Not all proxies are perceived the same way by online services. The type of network an IP belongs to also matters. For example, datacenter proxies use IP addresses owned by hosting providers. They typically offer high speed and stable connections, but services can more easily identify this traffic as coming from server infrastructure.
ISP proxies occupy a middle position. They are hosted on server infrastructure but use IP addresses assigned by internet service providers. Because of this, the traffic appears closer to regular user connections and attracts less attention from filtering systems.
Residential proxies, on the other hand, are associated with real user devices and home networks. As a result, they appear to services as normal user traffic.
For tasks involving a large number of requests or scaling API operations, datacenter proxies are often used due to their performance. However, when interacting with services that have stricter anti-fraud mechanisms, such IPs may receive restrictions more quickly.
Behavioral Traffic Analysis
Modern anti-fraud systems analyze not only the IP itself but also how requests behave.
Among the factors considered are:
- request frequency
- sequence of actions
- client type
- similarity to normal user behavior
Because of this, even a high-quality IP can become ineffective if the request structure looks suspicious.
This is particularly noticeable in scenarios such as:
- account automation
- bulk actions
- expanding operational workflows
In such cases, it is not only the pool of IP addresses that matters, but also the overall proxy usage architecture.
Geography and Regional Consistency
Another factor is the geographic consistency of the IP.
Many services check:
- the country of the IP
- the region
- the network ASN
- consistency with language and timezone
If requests originate from an unexpected region, even a valid IP may trigger additional verification checks.
For this reason, tasks such as localized testing or regional scraping often rely on residential proxies, which provide IP addresses from specific countries.
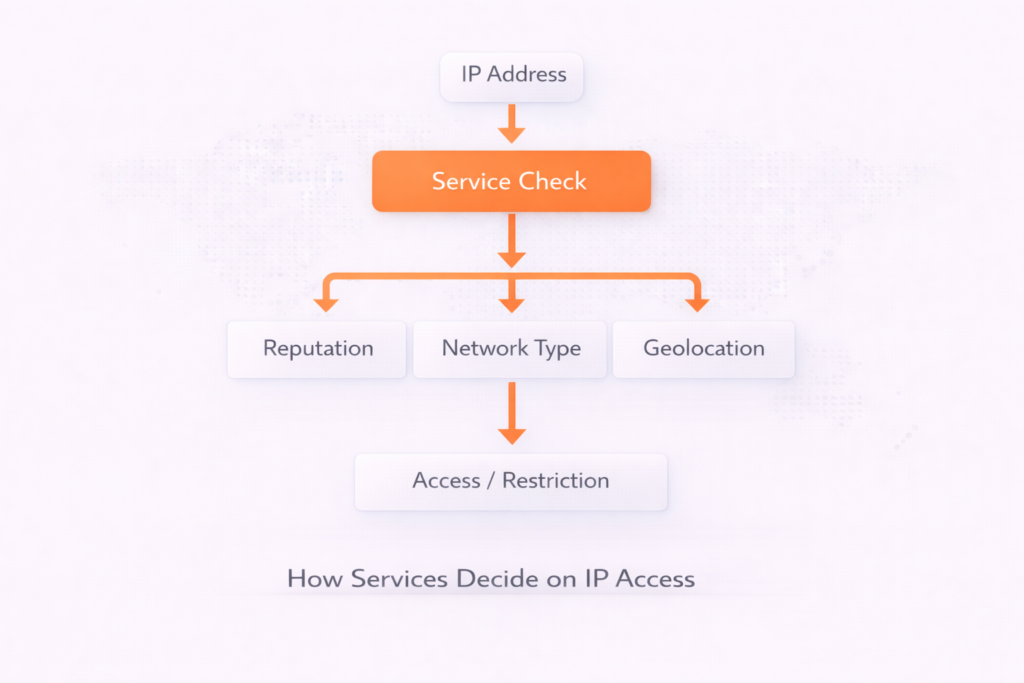
| Check | Why it matters |
| IP connectivity | Checks whether the proxy responds and a connection can be established |
| Network type / ASN | Helps determine whether the IP belongs to a datacenter, ISP, or residential network |
| IP reputation | Shows whether the address was previously used for suspicious or abusive activity |
| Geographic match | Ensures the IP country and region match the intended use case |
| Connection stability | Helps verify that the proxy can maintain stable sessions for longer tasks |
Practical Takeaways
IP validity is only the first level of evaluation. Real interaction with online services depends on a number of additional factors.
IP reputation plays an important role. If an IP has previously been used for large volumes of requests, account registrations, or other suspicious activities, services may trust it less and introduce restrictions more frequently.
Network type also matters. One type of proxy may work well for handling many requests, while the same IPs may face limitations when interacting with platforms that use stricter protection systems.
Traffic behavior is another important factor. If automated traffic appears unnatural, the likelihood of restrictions increases.
Finally, geographic consistency should also be considered. The country and region of the IP should match the intended usage scenario.
For this reason, professional proxy infrastructures do not treat proxies as isolated IP addresses but as part of a broader network architecture, where the combination of characteristics matters more than simple IP availability.
Conclusion
Working with proxies is not limited to checking whether an IP address is accessible. Even a valid IP may turn out to be useless if it does not match the requirements of a specific task.
This becomes particularly clear in scenarios involving automation, API interactions, or data scraping, where services analyze not only the IP itself but also how the connection is used.
In such cases, several factors need to be considered simultaneously: IP reputation, network type, geographic location, and request behavior. For example, the history of an IP address may influence the level of trust from online services. Network type also matters, as platforms react differently to server and user-based IPs. Additionally, the geographic location of the address should match the intended task, and the traffic should not appear overly repetitive or unusually intense.
For this reason, professional proxy systems are not built around individual IP addresses alone. Instead, they form part of a broader network infrastructure where both the origin of the address and the behavior of traffic are important. In such environments, proxy services like MangoProxy are typically used as one component of that infrastructure.

Frequently asked questions
Here we answered the most frequently asked questions.
Why does an IP work in a browser but not in a script?
Browsers generate complex and varied user behavior. Scripts often send repetitive requests, which can trigger restrictions.
Is it possible to determine IP usability in advance?
Partially. Basic parameters can be checked, but the final suitability depends on the specific service and usage scenario.
Why are datacenter IPs blocked faster?
Such IPs are easier to recognize as server infrastructure and are more commonly associated with automated activity.
When are residential proxies a better choice?
When it is important to imitate regular user traffic and reduce the likelihood of anti-fraud checks.
