Why IP Addresses Get Blocked So Quickly
One of the most common complaints in automation sounds familiar: “The IP worked for a few hours – and then it was blocked.” It often feels like the issue lies in the address itself or in its quality.
In reality, an IP is rarely blocked on its own. More often, the address becomes exposed due to behavioral patterns, traffic load, or architectural flaws. Anti-fraud systems analyze not only the traffic source but also how that traffic behaves.
Without understanding why an IP enters a risk zone, replacing addresses turns into an endless cycle without structural improvement.

1. IP as an Indicator, Not the Root Cause
An IP address is one of many signals in a risk evaluation model. When suspicious activity is detected, systems consider:
- request frequency and intensity,
- repetition of actions,
- digital fingerprint similarities,
- sudden geographic changes,
- signs of connection between accounts.
If large volumes of identical actions are executed through a single address, the IP becomes a marker of repetitive behavior. In this case, even high-quality proxies for automation will not help if the underlying logic remains uniform.
An IP ends up blocked not on its own, but because it carries a repeating pattern of activity.
2. Load and Request Intensity
One of the most common causes is overload.
During large-scale scraping or API usage, a single IP may generate hundreds of requests per minute. Even when using datacenter proxies that provide high speed, excessively high activity quickly triggers restrictions.
It is important to understand that anti-fraud systems evaluate not only volume, but also structure. Uniform intervals, lack of natural pauses, and identical scenarios all increase risk. When scaling, the goal is not simply to add more IPs, but to distribute load intelligently.
3. Identical Behavior Model
| Real User Behavior | Automated Model |
| Irregular action intervals | Fixed time intervals |
| Different browsing depth | Identical action sequence |
| Random pauses and returns | Strict linear logic |
| Variable reaction speed | Constant execution speed |
| Different entry points | Same starting URL |
| Scenario variability | Repeating action algorithm |
In account automation, a single logic model is often applied: identical actions, identical sequences, identical timing.
Even when residential proxies are used, the behavior may still look automated. The system links not only the IP, but also the pattern behind it.
This is especially visible in:
- account farming,
- warming advertising accounts,
- bulk interface actions,
- API integrations without variability.
In such setups, the IP acts as a technical intermediary rather than the actual cause of the block.
4. Geography and Consistency
Rapid regional switching is another risk factor. If an account appears from different countries or subnets within an hour, this creates an atypical network profile.
In some scenarios, ISP proxies provide a more logical solution, offering IP stability while maintaining characteristics of user-origin connections. This reduces the effect of abrupt network shifts. However, even in this case, maintaining behavioral consistency remains essential.
5. Account Linking
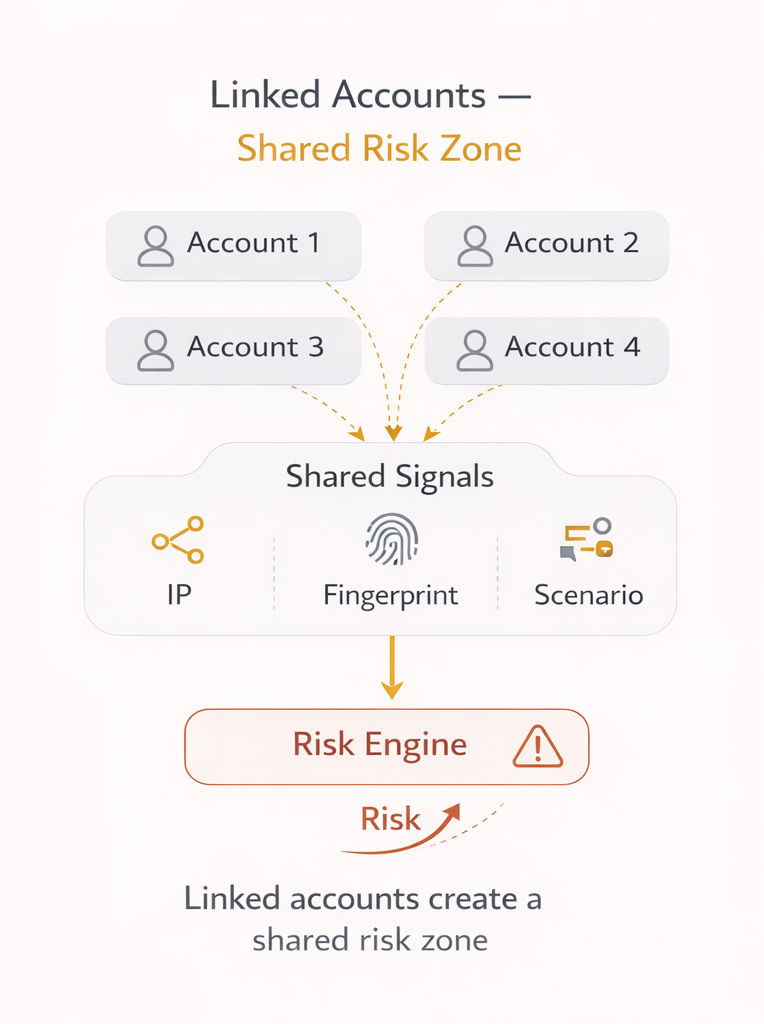
An IP is often blocked together with other addresses connected through shared activity.
If multiple accounts use identical technical parameters and repeat the same actions, anti-fraud systems associate them with each other. In such situations, simply changing the address is not enough. A properly designed proxy infrastructure with load separation and independent configuration of working profiles becomes critical.
Without technical separation, an IP becomes a shared risk zone.
Practical Takeaways
- IP is an indicator of activity, not the source of the problem.
- The main risk comes from repetitive actions.
- Overload and uniform workflows accelerate restrictions.
- Scaling requires proper load distribution and behavioral variability.
- Proxies should be part of a well-designed architecture, not a temporary fix.
In professional projects using solutions such as MangoProxy, proxies are treated as part of the network model integrated into the overall automation system.
Conclusion
IP addresses get blocked quickly not because of inherent quality issues, but because of how they are used. Anti-fraud systems evaluate behavior, load, and interconnections.
A systematic approach to automation allows you to manage risk effectively. The more carefully the architecture is designed, the longer IP addresses remain operational.

Frequently asked questions
Here we answered the most frequently asked questions.
Why does my IP get blocked so quickly?
Most often, the reason is high request intensity or repetitive actions. When the system detects a consistent pattern, it increases the risk level associated with the address.
Will constant IP rotation solve the issue?
If behavior remains the same, blocks will continue. Changing the address without changing the logic only provides a temporary effect.
Which type of proxy gets blocked less often?
Risk depends less on the type (datacenter, residential, or ISP) and more on how it is used.
Can blocks be completely avoided?
No. The goal is not total elimination, but reducing probability through sound architectural design.
