DNS Leaks: How Websites Identify the Real IP

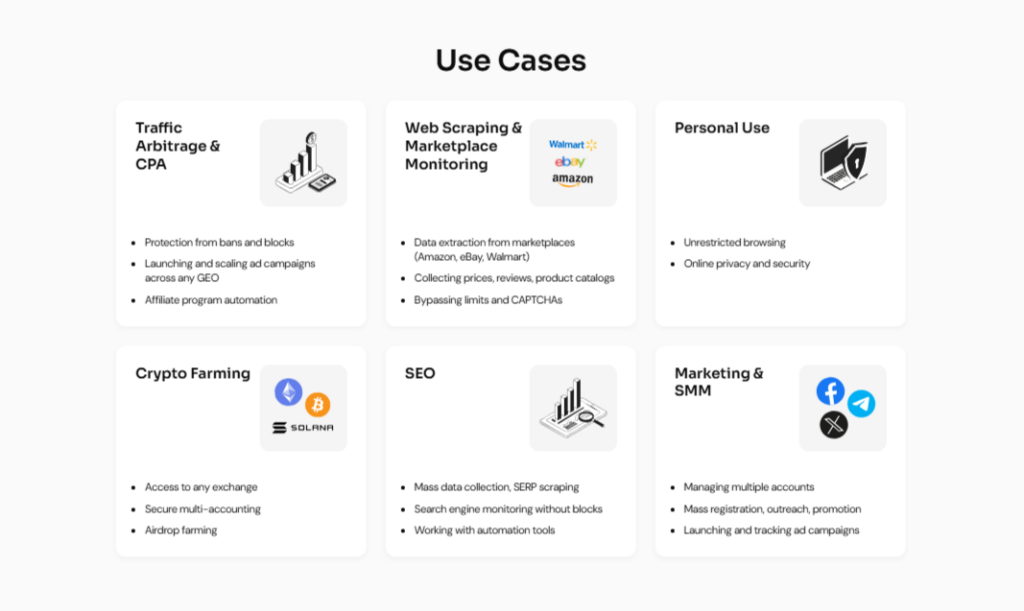
High-quality proxy servers are a must for professional marketers and data analysts for the effective performance of their tasks. They enable work teams to handle various accounts, carry out testing across different regions, support analytics workflows and keep a steady automation environment.
The expectation is simple: the target site must see the proxy IP. However, a hidden vulnerability frequently breaks this protection. Real IP addresses often “leak” not through the main data connection, but through a background process most users ignore. Even a transparent proxy, which operates without requiring client configuration, can be susceptible to DNS leaks if not properly managed.
This situation, referred to as a DNS leak, occurs when the IP address of the user is revealed to the website without the knowledge of the proxy server. The ability to control this system is what determines whether the connection is safe or unsafe.
How DNS Works
Network identity is also shaped by far more than a visible IP address. Even when web traffic is routed correctly, background requests may follow different paths. This is where silent exposure begins.
DNS leaks were once considered a niche technical issue. Today, as detection systems mature and correlation techniques improve, name resolution has become a first-class signal rather than a background detail. Platforms no longer look only at what you load, but at how your entire network environment behaves over time.
A DNS is a directory that converts the names of websites that people can easily understand into numerical addresses that computers can read. In this way, it helps the client locate the appropriate web server on the internet. Once DNS resolution is complete, the web server receives requests from the client to access the desired content.
How DNS Fits Into Network Traffic
DNS operates independently from browser traffic and often follows system-level routing. In an internal network, a forward proxy can be used to manage DNS queries and ensure they follow the correct routing path. When resolution paths do not match proxy traffic, this mismatch becomes a stable signal used by platforms to verify real network origin.
It is similar to a directory service. When a user types in a domain name, the system identifies the server that should handle the request. This lookup happens before any website content is delivered and sets the foundation for the entire session.
How DNS-Based IP Detection Works
Websites and anti-fraud systems use sophisticated techniques to validate traffic. They do not just look at the IP address sending the HTTP request, they analyze the entire connection footprint.
DNS is valuable to detection systems because it reflects behavior, not just configuration. While IP addresses can change quickly, DNS resolution patterns tend to remain consistent across sessions. Platforms observe where lookups originate, how often they repeat, and whether they align with traffic routing. DNS queries for specific web pages or pages can be correlated with traffic patterns to detect inconsistencies. A single mismatch rarely matters, but recurring inconsistencies gradually affect internal trust scoring.
Over time, this behavioral signal becomes more reliable than visible network attributes. Advanced tracking scripts force the browser to resolve a unique, custom sub-domain or even unique web pages controlled by the site.
If a leak occurs, the computer sends a query for this specific sub-domain using the real ISP’s resolver. The website’s server logs the incoming DNS request. It sees that the request came from a resolver located in Berlin, while the HTTP traffic comes from a proxy IP in New York.
This discrepancy acts as a red flag. The system concludes the user is masking their identity. The real location is likely the one associated with the background lookup, leading to immediate blocking.
How DNS Queries Affect Privacy
DNS queries reveal intent and context: which domains are accessed and from what type of network environment. When these lookups do not align with the proxy IP, mixed signals appear. The function of DNS queries in this context is to provide platforms with behavioral signals that can compromise privacy. This mismatch often produces a false sense of safety, where everything appears correct on the surface while background traffic quietly exposes inconsistencies.
Over time, these signals accumulate. Even when individual sessions appear clean, long-term activity builds a behavioral profile based on resolution consistency. This is why DNS-related exposure often affects mature accounts and scaled workflows rather than single sessions.
Unlike browser fingerprints, DNS resolution patterns change slowly. Even when IPs rotate and profiles reset, resolvers often remain stable across sessions. This persistence allows platforms to correlate activity over time, turning minor inconsistencies into long-term identifiers.
What is a DNS leak?
A leak occurs when the operating system bypasses the active proxy connection and sends queries directly. In this case, the system is connecting directly to the DNS resolver, exposing the real IP. This usually happens when system-level settings take precedence over browser configuration. Web traffic follows the proxy, but address resolution continues using default servers.
In browser-based scenarios, leaks often occur when extensions or profiles are isolated, but resolution remains shared. The browser appears clean, yet name lookups still reflect the underlying system network.
At the system level, DNS leaks emerge when background services, update checks, or auxiliary processes resolve domains independently of the main session. These requests add noise that platforms can correlate over time.
Mixed environments create another common scenario. Multiple profiles, automation tools, and parallel sessions may share DNS infrastructure while rotating proxy IPs. This combination produces patterns that are difficult to hide. A properly configured proxy can act as a single point of control for DNS queries, reducing the risk of leaks.
Why Proxies Require Proper Configuration
A proxy only protects traffic that actually passes through it. The proxy acts as an intermediary, forwarding requests between the client and the destination server. When DNS resolution escapes that path, it becomes a partial shield rather than a complete one.

Assuming that reliable proxies handle all network isolation is a misconception — they manage traffic routing, not total masking. Any process operating outside that boundary inherits the system’s native network behavior. Without alignment across layers, its usage becomes fragmented rather than protective.
How Websites Determine the Real IP Address Through DNS
DNS is a particularly attractive signal for detection systems because it is consistent, difficult to spoof casually, and rich in contextual data. These queries expose resolver location, network ownership, timing patterns, and routing behavior.
Repeated mismatches gradually affect internal trust scoring, leading to increased verification prompts and subtle restrictions
The behavior also allows platforms to identify shared infrastructure. Even when browser fingerprints differ, patterns in name resolution can reveal common paths across multiple sessions. For example, a reverse proxy server can be deployed within a private network to manage incoming requests and forward them to backend servers. A reverse proxy accepts requests from clients and then forwards requests to the appropriate web server, optimizing both performance and security. Reverse proxies can also interact with other devices and web filters to control and monitor network traffic.
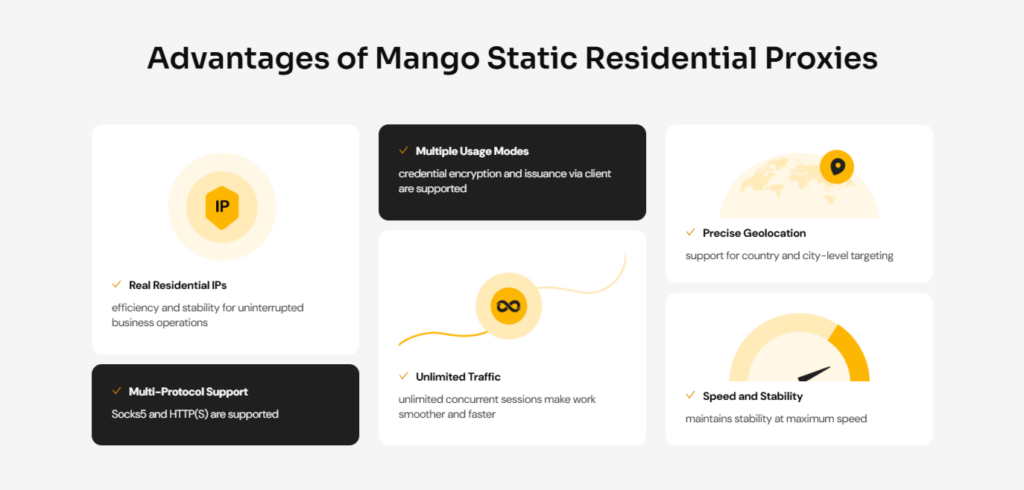
This is why large proxy infrastructures such as Mango Proxy focus on maintaining consistency between IP pools and DNS behavior across regions. At scale, small mismatches accumulate quickly and become visible.
The consequences are often delayed. Instead of immediate bans, platforms apply invisible degradation: slower approvals, reduced reach, or unstable account behavior. Background leaks distort analytics as well, causing regional logic to behave unpredictably and undermining controlled testing.
Risks Associated With DNS Leaks
The danger of DNS leaks lies in their subtlety. DNS leaks pose significant security risks by exposing sensitive information, such as your real IP address or browsing activity, to third parties. They do not break sessions or cause obvious errors. Instead, they quietly weaken network trust. For example, a DNS leak can reveal your true location to a website, leading to account suspension or data exposure if the site detects proxy use or policy violations.
- Loss of anonymity through network correlation
- Account suspensions and forced re-verification
- Incorrect regional targeting and testing errors
- Data inconsistency during scraping and monitoring
Because the resolution process operates in the background, its signals are often trusted more than surface-level indicators. Once inconsistencies are recorded, they are difficult to undo, making this one of the most persistent exposure vectors.
How to Reduce the Risk of DNS Leaks
To stop leaks, one has to use properly configured software and also rely on top infrastructure. Relying solely on default settings guarantees exposure.
At the configuration level, DNS resolution must follow the same network path as web traffic. System, browser and proxy settings need to reinforce each other rather than operate independently.
Unreliable resolvers change routing dynamically, increasing the likelihood of mismatches. High-quality proxy servers depend on predictable resolution behavior as much as IP rotation.
Operationally, safety is an ongoing process. New tools, profiles, or workflows can reintroduce leaks without obvious signs. Teams that understand how to avoid DNS leaks treat network consistency as a routine check, not a one-time setup.
Choosing the right infrastructure is equally critical. High-quality proxy servers ensure that DNS requests are handled within the same network as the data traffic. Using an SSL proxy with SSL encryption (Secure Sockets Layer) ensures that both DNS requests and data traffic are encrypted for maximum security. Residential proxies are particularly effective for maintaining privacy and avoiding detection. This is where The Mango Proxy service demonstrates value.
By providing a vast pool of ethical, clean IPs, its infrastructure supports consistent privacy. With 90M+ IP addresses across 200+ locations, users can ensure their DNS path matches their data path. Reliable proxies do not just mask the IP, they ensure the entire connection profile appears organic.
Web proxies, including free web proxy services, allow users to browse popular websites like Google and Facebook securely and anonymously. Some providers even offer free web proxy options for users who want to browse the internet without cost.
For teams relying on proxies, DNS awareness transforms proxy usage from a fragile workaround into a stable operational foundation.
Comparison to Other Online Privacy Tools
When it comes to safeguarding online privacy and masking your real IP address, users have several options-each with its own strengths and limitations. The most common tools include proxy servers, Virtual Private Networks (VPNs), and Tor browsers. Understanding how these solutions handle web traffic, DNS queries, and network identity is essential for anyone seeking to protect sensitive information or access restricted content.
Proxy Servers act as intermediaries between your device and the destination website. By forwarding web requests through a proxy server, users can hide their real IP address and appear to be browsing from a different location. Solutions like MangoProxy offer advanced features such as residential proxies, IP rotation, and geolocation targeting, making them ideal for businesses managing multiple accounts, web scraping, or automating web activity. However, unless configured at the system level, some web browsers or applications may still send DNS queries outside the proxy path, risking DNS leaks and exposing the real IP address.
VPNs (Virtual Private Networks) encrypt all internet traffic from your device and route it through a secure server in a specific country or region. This provides a higher level of privacy by masking both your IP address and encrypting data, making it difficult for third parties to monitor your internet activity. VPNs are effective at preventing DNS leaks when they include DNS leak protection, ensuring that all DNS requests are handled within the encrypted tunnel. However, VPNs can sometimes slow down web browsing speeds and may not offer the granular control over IP rotation or geolocation that specialized proxy services provide.
Tor Browsers use a decentralized network of volunteer-operated nodes to anonymize web traffic. Each web request is routed through multiple relays, making it extremely difficult to trace the origin of the connection. Tor is highly effective for anonymity but is generally slower than both proxies and VPNs, and may not be suitable for high-volume web scraping or business automation. Additionally, some websites block Tor exit nodes, limiting access to popular websites and services.
While all these tools enhance online privacy and help mask your real IP address, they differ in how they handle DNS queries and web traffic. Proxy servers, especially when used with proper configuration and reliable infrastructure, offer flexibility and performance for business use cases. VPNs provide strong encryption and system-wide protection, while Tor maximizes anonymity at the cost of speed and compatibility.
Ultimately, the effectiveness of any privacy tool depends on how well it integrates DNS resolution with web traffic routing. Even the most secure proxy or VPN can be undermined by a DNS leak, exposing your real IP address to the destination website. For organizations and individuals who require robust, scalable, and consistent privacy-especially when managing many devices or accessing restricted content-choosing a provider like MangoProxy ensures that both web requests and DNS queries are handled securely, minimizing the risk of exposure and maintaining true online anonymity.
Conclusion
DNS leaks represent a silent threat to digital privacy. A user can invest heavily in tools, yet fail due to a simple configuration oversight. Websites utilize these leaks as a primary method to identify and block proxy users.
Verification of settings remains the most effective defense. Regular tests ensure that the resolution address matches the proxy location. Ultimately, the combination of technical vigilance and the use of a robust provider like Mango Proxy creates a watertight defense, protecting the real IP from detection.

Very helpful article it finally made clear why issues can occur even when using proxies and what really needs attention.