How Websites Determine IP Quality

When working with proxies, many people start by checking the simplest thing – whether the IP address responds to a request. If a connection is established and the server returns a valid response, the proxy is usually considered functional.
However, in practice this is not always enough. An IP may easily pass basic checks and appear completely valid. But once real activity begins, restrictions can appear quite quickly. CAPTCHAs may start showing up, responses from the website become slower, and in some cases access is blocked altogether.
This situation is especially noticeable in automation tasks, when working with APIs, or when performing large-scale data collection. In these cases, websites evaluate more than just whether a connection exists. They also analyze how the IP address is used – including request frequency, traffic behavior, and other signals.
These factors directly affect how long an IP address can operate without triggering additional checks. That is why one proxy may work reliably, while another starts facing restrictions almost immediately.
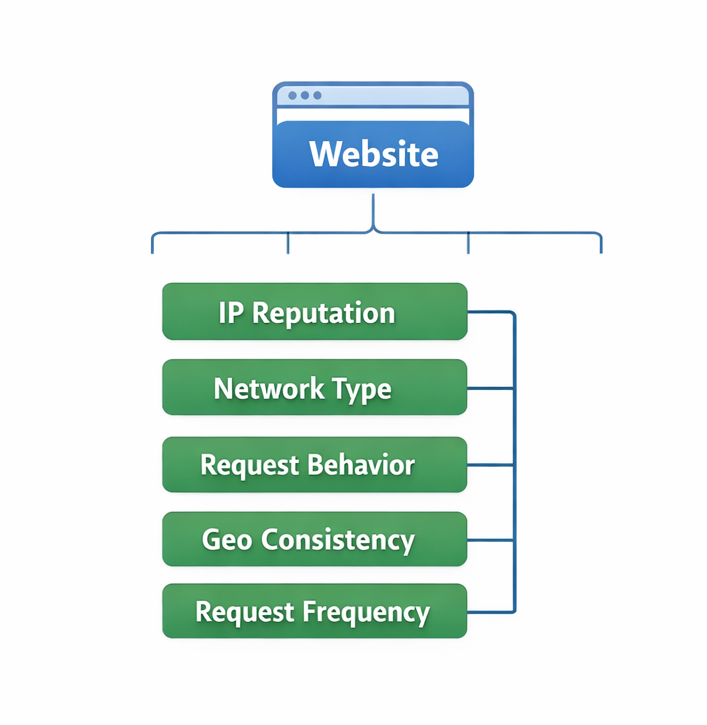
How Websites Evaluate an IP Address
Modern anti-fraud systems rarely make decisions based on a single parameter. Instead, they analyze a combination of signals that help determine where an IP address comes from and how it behaves on the network.
IP Reputation
One of the first things many websites check is the history of an IP address.
If the address has previously been involved in mass requests, website scanning, or suspicious activity, it may appear in various reputation databases. In this case, even a properly configured proxy may immediately trigger stricter verification.
This is why in scenarios where proxies for scraping are used, it is important to consider not only connection speed but also the previous usage history of the IP address.
Network Origin
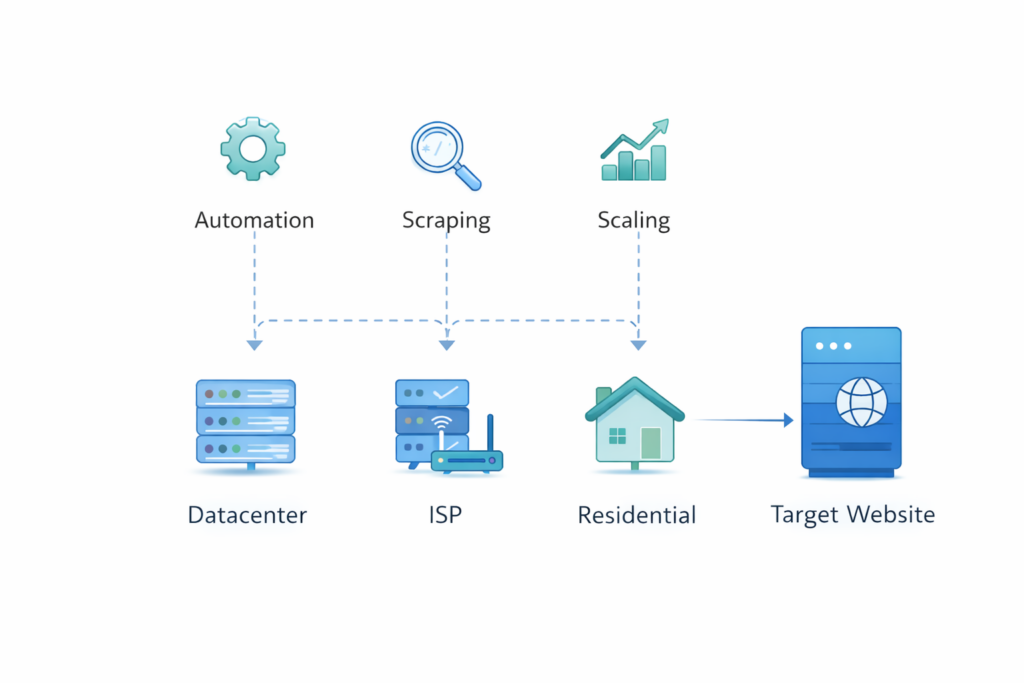
Another important factor is the network from which the IP address originates. Websites can often determine whether an IP belongs to a datacenter, an ISP network, or a real user device. This directly influences the level of trust assigned to the connection.
Datacenter proxies are usually easy to detect because they belong to hosting providers. They are well suited for tasks involving large numbers of technical requests, but they may face stricter limitations.
ISP proxies occupy a middle ground. They operate through server infrastructure but use IP ranges assigned to internet service providers, which often makes them appear more natural to websites.
Residential proxies typically have the highest level of trust because their IP addresses are associated with real consumer networks.
Behavioral Signals
Even if an IP appears “clean,” the system may still analyze how requests are made.
For example:
- request frequency
- traffic consistency
- sequence of actions
- distribution of requests over time
If a large number of requests come from the same IP within a short period, the system may classify such traffic as automated.
For this reason, when scaling operations it is important to consider not only the proxy type but also the architecture used to distribute traffic.
Geography and Parameter Matching
Websites also check whether the IP address matches other connection parameters.
For example:
- IP geolocation
- browser language
- time zone
- account region
If these parameters differ significantly, the anti-fraud system may reduce the trust level of the connection. In environments that involve multi-account setups or automation, maintaining this consistency can play an important role.
IP Reuse
Another factor is how many users operate through the same IP address. If a single address is used by many clients at the same time, its behavioral profile becomes less natural. As a result, even high-quality proxies may encounter restrictions more quickly. For long-term operations, many projects try to rely on more stable IP allocation and avoid excessive overlap between sessions.
Practical Takeaways
When choosing proxies, it is important to understand that websites evaluate more than just whether an IP address is accessible.
IP quality is influenced by several factors:
- network origin
- IP usage history
- traffic behavior
- load distribution
- geographic consistency of parameters
The stability of an infrastructure therefore depends not only on the type of IP addresses being used but also on how they are managed overall. In automation and scaling environments, different proxy types are often used together – for example datacenter, ISP, and residential proxies. Each of them is suited for different scenarios and solves a specific part of the workload.
Conclusion
The quality of an IP address cannot be determined by a single metric. In practice, it is the result of multiple factors that websites evaluate simultaneously. These include network origin, IP usage history, traffic behavior, and many other signals that help anti-fraud systems assess the reliability of a connection.
For this reason, stable proxy usage depends not only on the type of IP address but also on how the overall infrastructure is designed – including traffic distribution, proxy management, and the general approach to network operations.

Frequently asked questions
Here we answered the most frequently asked questions.
Why can an IP work but still receive CAPTCHAs?
Even if the IP responds correctly, the system may detect suspicious traffic behavior. Frequent requests or unusual patterns can trigger additional verification.
Are residential IPs always better?
Not necessarily. They often appear more natural to websites but may be less stable for certain technical workloads.
Is it possible to completely avoid blocks?
No. Protection systems evolve over time. The goal of infrastructure is to reduce the likelihood of restrictions, not eliminate them completely.
Why do different websites react differently to the same IP?
Each platform uses its own anti-fraud mechanisms and reputation databases. Because of this, the same IP address may be evaluated differently across services.
