What Is a Proxy Server?

A proxy server is an intermediary system that forwards internet requests between a user and a destination website. Instead of connecting directly to online services, traffic is routed through a proxy node that communicates with the target server on behalf of the client.
Because of this architecture, proxy servers can influence how requests appear to websites, distribute traffic across multiple IP addresses, and enable controlled network execution strategies.
Proxy infrastructure plays an important role in modern digital operations such as data collection, automation workflows, cybersecurity testing, and localized content verification.
Quick Answer: What Does a Proxy Server Do
A proxy server:
- hides the original IP address
- routes traffic through another network endpoint
- enables geographic targeting
- helps distribute large request volumes
- supports automation systems
In simple terms:
A proxy server changes the visible identity of a network connection.
How Proxy Servers Work
When a device uses a proxy server, the communication flow differs from direct browsing.
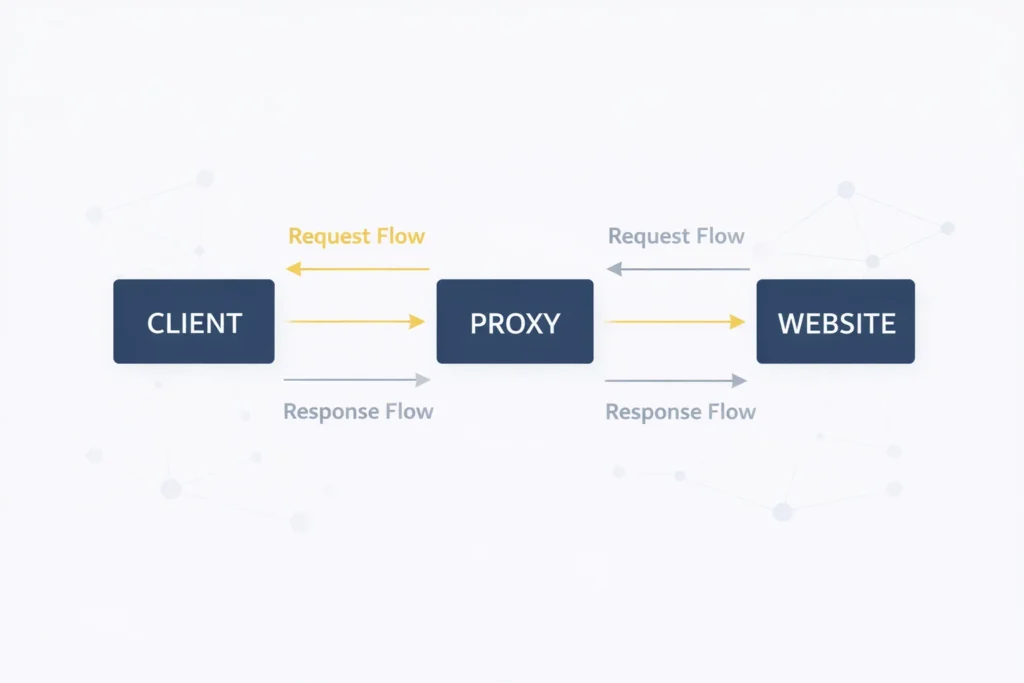
A typical proxy request sequence looks like this:
- A user sends a request to a proxy server
- The proxy assigns or uses an available IP address
- The request is forwarded to the destination website
- The website responds to the proxy
- The proxy delivers the response back to the user
This intermediary routing model allows proxy servers to perform additional actions such as filtering requests, caching content, or modifying headers.
Why Proxy Servers Are Used
Organizations deploy proxy infrastructure for several operational reasons.
Traffic Distribution
Automation systems often require parallel request execution. Proxy pools enable traffic to be distributed across multiple network identities.
Regional Access Simulation
Businesses monitoring localized search results or pricing data rely on proxies to simulate connections from specific locations.
Data Collection
Large-scale scraping workflows depend on proxy routing to reduce rate-limit triggers and maintain access continuity.
Network Segmentation
Different proxy endpoints can be assigned to separate workloads to reduce overlap signals.
Types of Proxy Servers
Modern proxy ecosystems include several infrastructure categories.
| Proxy Type | IP Origin | Main Advantage | Typical Usage |
| Residential | ISP consumer networks | realistic traffic signals | scraping |
| Datacenter | Cloud infrastructure | high performance | automation |
| ISP | Hosted ISP ranges | session stability | account workflows |
| Mobile | Cellular networks | dynamic behavior | social platforms |
Each proxy type provides a different balance between authenticity, speed, and scalability.
Residential Proxies
Residential proxies use IP addresses associated with real internet subscribers. Because these connections resemble typical browsing activity, platforms often treat requests as legitimate user traffic.
They are commonly used for:
- localized market research
- ad visibility verification
- SERP monitoring
- competitor data analysis
Datacenter Proxies
Datacenter proxies originate from server hosting environments. They offer fast response times and can support high request volumes.
Typical use cases include:
- large-scale crawling
- account automation
- load testing
- API interaction pipelines
ISP Proxies
ISP proxies combine characteristics of residential and datacenter infrastructure. They provide static IP identities with server-grade routing performance.
They are often used in workflows that require persistent connections.
Mobile Proxies
Mobile proxies route traffic through carrier networks. Because mobile IP assignment patterns change frequently, requests may appear more organic to detection systems.
They are used in:
- mobile app testing
- social automation
- sensitive scraping environments
Proxy vs Direct Connection
| Feature | Direct Connection | Proxy Connection |
| IP visibility | Real IP | Proxy IP |
| Traffic routing | Single path | Distributed |
| Scalability | Limited | High |
| Identity control | Low | High |
Proxy routing introduces flexibility in how network requests are executed.
Proxy vs VPN
Although both proxies and VPNs route traffic through intermediary systems, their purpose differs.
| Feature | Proxy | VPN |
| Encryption | Optional | Built-in |
| IP rotation | Supported | Rare |
| Automation compatibility | High | Low |
| Security focus | Moderate | High |
VPN solutions prioritize secure connectivity, while proxies are optimized for traffic distribution and execution scaling.
Proxy Infrastructure at MangoProxy
MangoProxy provides multiple proxy network types designed for scalable digital operations.
Residential proxy networks help access region-specific data with realistic traffic patterns.
ISP proxy solutions support long-duration sessions in automation frameworks.
Datacenter proxy clusters enable high-throughput request execution.
Mobile proxy routing environments help manage sensitive interaction workflows.
Combining proxy categories can significantly improve operational reliability.
Key Takeaways
- proxy servers act as intermediaries between clients and websites
- proxy infrastructure enables distributed request execution
- different proxy types support different performance profiles
- proxy routing is essential for automation and large-scale data workflows
Glossary
Proxy Node – A server that forwards internet requests on behalf of a client.
IP Rotation – Switching between multiple IP addresses during traffic execution.
Traffic Routing – Directing requests through alternative network paths.
Session Persistence – Maintaining the same connection identity over time.

Frequently asked questions
Here we answered the most frequently asked questions.
What is the main purpose of a proxy server?
To route requests through another IP address and control how connections appear to websites.
Are proxy servers legal?
Yes, proxy technology is widely used for legitimate operational purposes.
Do proxies encrypt traffic?
Not always. Encryption depends on proxy configuration and protocol.
Which proxy type is best?
The optimal proxy type depends on whether authenticity, speed, or session stability is the priority.
