429 Too Many Requests: How to Avoid Rate Limits When Using Proxies

The 429 Too Many Requests response is one of the most common problems developers encounter when collecting data from websites or running automated tasks.
This status code indicates that a server has received too many requests from the same client within a defined time window. Instead of processing additional traffic, the system temporarily blocks further requests.
For scraping systems, this often happens when request frequency, IP reputation or session behavior triggers rate-limiting mechanisms.
Understanding how rate limits work allows engineers to design more stable automation pipelines and prevent unnecessary blocking.
Key Takeaways
- a 429 response indicates the server has detected excessive request activity
- rate limits usually depend on request frequency per IP address
- distributing traffic across multiple identities reduces blocking risk
- introducing realistic delays between requests improves stability
- combining rotation and session management often produces better results
What the 429 Status Code Means
HTTP status code 429 signals that the client has exceeded a server-defined request threshold.
Unlike other errors, this response usually indicates temporary blocking rather than permanent access denial.
| Status Code | Meaning |
| 403 | server intentionally denies access |
| 404 | requested resource not found |
| 429 | too many requests detected |
Many platforms enforce rate limits to protect infrastructure from abuse, automated scraping or excessive traffic spikes.
Why Websites Use Rate Limiting
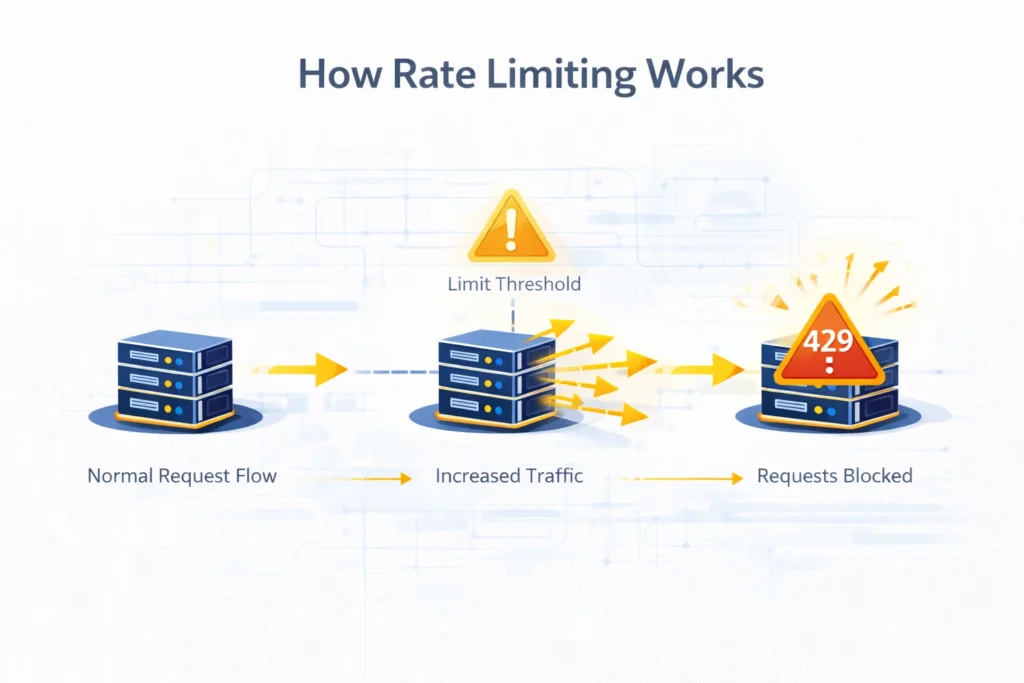
Rate limiting is a defensive technique that prevents servers from being overloaded.
It also helps detect automated traffic patterns.
Common objectives include:
- protecting server resources
- preventing automated data extraction
- reducing bot activity
- maintaining fair usage among users
Platforms often implement several layers of rate-limiting logic simultaneously.
Common Signals That Trigger 429 Errors
Servers typically analyze several indicators before triggering rate limits.
| Detection Signal | Explanation |
| Request frequency | too many requests within a short period |
| IP concentration | large traffic volume from one address |
| parallel connections | multiple simultaneous sessions |
| repetitive patterns | identical request sequences |
When these signals exceed predefined thresholds, the server temporarily restricts further access.
👉 See how traffic patterns trigger blocks in Proxy Detection Guide
How Rate Limits Work
Different platforms implement different request thresholds.
For example:
| Request Speed | Detection Risk |
| 1–2 requests/sec | low |
| 5–10 requests/sec | moderate |
| 20+ requests/sec | high |
These values vary widely depending on the website.
Large platforms often use adaptive algorithms that dynamically adjust limits based on traffic patterns.
How to Avoid 429 Errors
Distribute Traffic Across Multiple IPs
Instead of sending all requests from a single address, scraping systems should distribute requests across multiple identities.
This prevents traffic concentration.
👉 Traffic distribution is explained in IP Rotation Explained
Rotating IP pools help simulate independent users rather than a single automated system.
Introduce Randomized Delays
Automated scripts often send requests in perfectly timed intervals.
Such behavior is easily detected.
Randomized delays between requests create patterns closer to normal browsing behavior.
Example pacing strategy:
| Delay Pattern | Effect |
| fixed interval | easier detection |
| randomized delay | lower detection risk |
| adaptive pacing | most realistic traffic pattern |
Reduce Parallel Requests
Sending too many simultaneous connections from the same address may trigger rate limits quickly.
Instead of parallelizing aggressively, distribute connections across multiple routing endpoints.
Use High-Trust Network Types
Traffic originating from certain network environments may receive stricter scrutiny.
Higher trust connection types often achieve better success rates.
| Network Type | Typical Rate Limit Tolerance |
| datacenter networks | moderate |
| ISP networks | high |
| residential connections | very high |
| mobile carrier networks | very high |
👉 Learn proxy identity differences in Residential vs Datacenter vs ISP vs Mobile Proxies
Session-Aware Scraping
Some platforms apply rate limits based on user sessions rather than IP addresses.
Maintaining cookies and consistent browsing flows can help reduce suspicious signals.
Stable routing environments are particularly useful for authenticated scraping workflows.
Monitoring and Diagnostics
Before modifying scraping logic, it is important to verify how the connection appears from the website’s perspective.
Important checks include:
- visible IP address
- geographic location
- network provider classification
Tools such as What Is My IP and IP Lookup can help confirm that requests originate from the expected environment.
Example Rate-Limit-Resistant Scraping Architecture
Large-scale data collection systems typically combine several routing strategies.
| Scraping Stage | Strategy |
| initial discovery | rotating residential connections |
| high-volume extraction | datacenter pools |
| session workflows | stable ISP routing |
| sensitive targets | mobile networks |
👉 See infrastructure strategies in Best Proxy for Web Scraping
This layered architecture distributes traffic and reduces the likelihood of rate-limit responses.
Final Thoughts
A 429 Too Many Requests response usually indicates that the server has detected excessive request activity within a defined time window.
Instead of repeatedly retrying blocked requests, engineers should analyze request pacing, routing distribution and session behavior.
Adjusting these factors helps stabilize automation workflows and maintain reliable access to target websites.
Glossary
Rate Limiting
A mechanism used by servers to restrict excessive traffic within a defined time period.
Request Frequency
The number of requests sent to a server over a specific interval.
Traffic Distribution
Spreading requests across multiple network identities to prevent concentration.
Session Persistence
Maintaining the same browsing identity during a connection session.
IP Rotation
Automatically switching outgoing IP addresses to simulate independent users.

Frequently asked questions
Here we answered the most frequently asked questions.
What does 429 Too Many Requests mean?
It indicates that the server received more requests from a client than allowed within a specific time window.
Can proxies prevent 429 errors?
Yes. Distributing requests across multiple IP addresses reduces traffic concentration and helps avoid rate limits.
How many requests per second are safe?
This depends on the target platform, but slower request rates usually reduce detection risk.
Is rotation necessary for scraping?
Automatically switching outgoing IP addresses to simulate independent users.
